SonarQube SonarScanner reference for STO
You can run scans and ingest results from SonarQube SonarScanner to analyze your code repos and ensure that they are secure, reliable, readable, and modular, among other key attributes.
Important notes for running SonarQube scans in STO
- STO supports repository scanning only for SonarScanner.
- STO supports all languages supported by SonarScanner.
- Before you scan your repo, make sure that you perform any prerequisites for the language used in your repo. For details about specific language requirements, go to the SonarQube language reference.
- By default, STO allocates 500Mi memory for the Sonarqube scan container. This should be enough for Ingestion scans. For Orchestration and Extraction scans, Harness recommends that you allocate at least 2GB for the container. You can customize resource limits in the Set Container Resources section of the SonarQube scan step.
- You need to run the scan step with root access if you need to add trusted certificates to your scan images at runtime.
- You can set up your STO scan images and pipelines to run scans as non-root and establish trust for your own proxies using self-signed certificates. For more information, go to Configure STO to Download Images from a Private Registry.
For more information
The following topics contain useful information for setting up scanner integrations in STO:
SonarQube step settings for STO scans
The recommended workflow is to add a SonarQube step to a Security Tests or CI Build stage and then configure it as described below.
A Docker-in-Docker background step is not required for this workflow.
Scan
Scan Mode
- Orchestration Configure the step to run a scan and then ingest, normalize, and deduplicate the results.
- Extraction Configure the step to extract scan results from an external SaaS service and then ingest, normalize, and deduplicate the data.
- Ingestion Configure the step to read scan results from a data file and then ingest, normalize, and deduplicate the data.
Scan Configuration
The predefined configuration to use for the scan. All scan steps have at least one configuration.
Target
Type
-
Repository Scan a codebase repo.
In most cases, you specify the codebase using a code repo connector that connects to the Git account or repository where your code is stored. For information, go to Configure codebase.
Name
The identifier for the target, such as codebaseAlpha or jsmith/myalphaservice. Descriptive target names make it much easier to navigate your scan data in the STO UI.
It is good practice to specify a baseline for every target.
Variant
The identifier for the specific variant to scan. This is usually the branch name, image tag, or product version. Harness maintains a historical trend for each variant.
Workspace
The workspace path on the pod running the scan step. The workspace path is /harness by default.
You can override this if you want to scan only a subset of the workspace. For example, suppose the pipeline publishes artifacts to a subfolder /tmp/artifacts and you want to scan these artifacts only. In this case, you can specify the workspace path as /harness/tmp/artifacts.
Ingestion File
The path to your scan results when running an Ingestion scan, for example /shared/scan_results/myscan.latest.sarif.
-
The data file must be in a supported format for the scanner.
-
The data file must be accessible to the scan step. It's good practice to save your results files to a shared path in your stage. In the visual editor, go to the stage where you're running the scan. Then go to Overview > Shared Paths. You can also add the path to the YAML stage definition like this:
- stage:
spec:
sharedPaths:
- /shared/scan_results
Authentication
Domain
The URL of the SonarQube server. Required for Orchestration and Extraction scans. This value corresponds to the sonar.host.url setting in SonarQube.
The fully-qualified URL to the scanner.
Enforce SSL
The step and the scanner communicate over SSL by default. Set this to false to disable SSL (not safe).
Access Token
The access token to log in to the scanner. In most cases this is a password or an API key.
You should create a Harness text secret with your encrypted token and reference the secret using the format <+secrets.getValue("project.my-access-token")>. For more information, go to Add and Reference Text Secrets.
Harness recommends that you use a SonarQube user token that includes permissions to run scans and to create projects.
If you use a project token, you must have access to the SonarQube project that you want to scan.
For more information, go to Generating and using tokens in the SonarQube documentation.
Scan Tool
Exclude
If you want to exclude some files from a scan, you can use this setting to configure the sonar.exclusions in your SonarQube project. For more information, go to Narrowing the Focus in the SonarQube docs.
Java Libraries
A comma-separated list of paths to files with third-party libraries used by your tests. For SonarQube scans, this corresponds to the sonar.java.libraries parameter.
Java Binaries
A comma-separated list of paths to the folders with the bytecode files you want to scan. For SonarQube scans, this corresponds to the sonar.java.binaries parameter.
Log Level, CLI flags, and Fail on Severity
Log Level
The minimum severity of the messages you want to include in your scan logs. You can specify one of the following:
- DEBUG
- INFO
- WARNING
- ERROR
Additional CLI flags
You can add CLI flags to run the sonar-scanner binary with specific command-line arguments. For example, suppose the scan is experiencing timeouts due to long response times from a web service. The following flag increases the timeout window: -sonar.ws.timeout 300
Fail on Severity
Every Security step has a Fail on Severity setting. If the scan finds any vulnerability with the specified severity level or higher, the pipeline fails automatically. You can specify one of the following:
CRITICALHIGHMEDIUMLOWINFONONE— Do not fail on severity
The YAML definition looks like this: fail_on_severity : critical # | high | medium | low | info | none
Additional Configuration
In the Additional Configuration settings, you can use the following options:
Advanced settings
In the Advanced settings, you can use the following options:
Security step settings for SonarQube scans in STO (legacy)
You can set up SonarQube scans using a Security step, but this is a legacy functionality. Harness recommends that you use an SonarQube step instead.
Docker-in-Docker requirements
The following use cases require a Docker-in-Docker background step in your pipeline:
- Container image scans on Kubernetes and Docker build infrastructures
- Required for Orchestration and Dataload scan modes
- Security steps (not step palettes) on Kubernetes and Docker build infrastructures
- Required for all target types and Orchestration/DataLoad modes
The following use cases do not require Docker-in-Docker:
- Harness Cloud AMD64 build infrastructures
- SAST/DAST/configuration scans that use scanner templates (not Security steps)
- Ingestion scans where the data file has already been generated
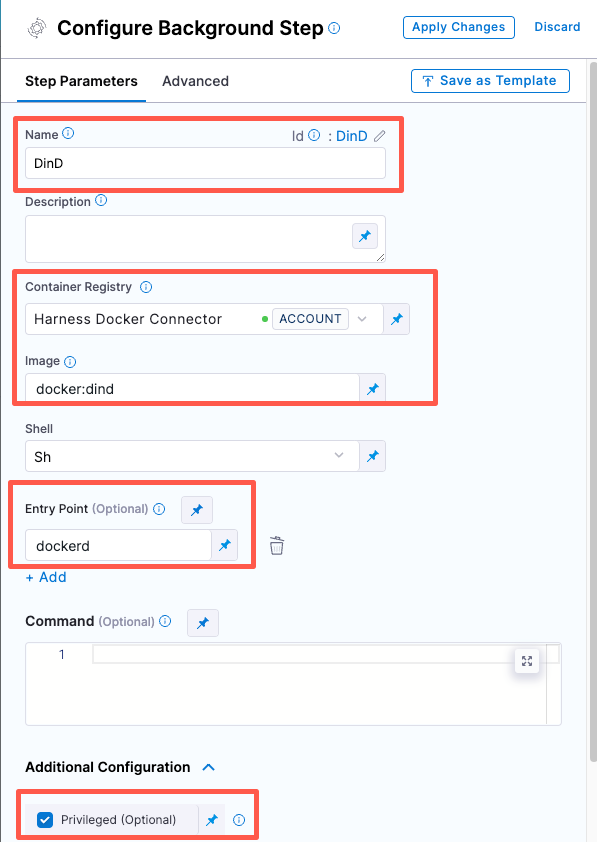
Set up a Docker-in-Docker background step
-
Go to the stage where you want to run the scan.
-
In Overview, add the shared path
/var/run. -
In Execution, do the following:
-
Click Add Step and then choose Background.
-
Configure the Background step as follows:
-
Dependency Name =
dind -
Container Registry = The Docker connector to download the DinD image. If you don't have one defined, go to Docker connector settings reference.
-
Image =
docker:dind -
Under Entry Point, add the following:
dockerdIn most cases, using
dockerdis a faster and more secure way to set up the background step. For more information, go to the TLS section in the Docker quick reference.
If the DinD service doesn't start with
dockerd, clear the Entry Point field and then run the pipeline again. This starts the service with the default entry point.- Under Optional Configuration, select the Privileged checkbox.
-
-
- Visual setup
- YAML setup
Add a Background step to your pipeline and set it up as follows:
- step:
type: Background
name: background-dind-service
identifier: Background_1
spec:
connectorRef: CONTAINER_IMAGE_REGISTRY_CONNECTOR
image: docker:dind
shell: Sh
entrypoint:
- dockerd
privileged: true
Scan modes
STO supports the following scan modes for SonarQube:
orchestratedScan— A Security step in the pipeline runs the scan and ingests the results. This is the easiest method to set up and support scans with default or predefined settings.dataLoad— The pipeline downloads scan results using the SonarScanner API.ingestionOnly— Run the scan in a Run step, or outside the pipeline, and then ingest the results. This is useful for advanced workflows that address specific security needs. See Ingest scan results into an STO pipeline.
Target and variant
The following settings are required for every Security step:
target_nameA user-defined label for the code repository, container, application, or configuration to scan.variantA user-defined label for the branch, tag, or other target variant to scan.
Make sure that you give unique, descriptive names for the target and variant. This makes navigating your scan results in the STO UI much easier.
You can see the target name, type, and variant in the Test Targets UI:
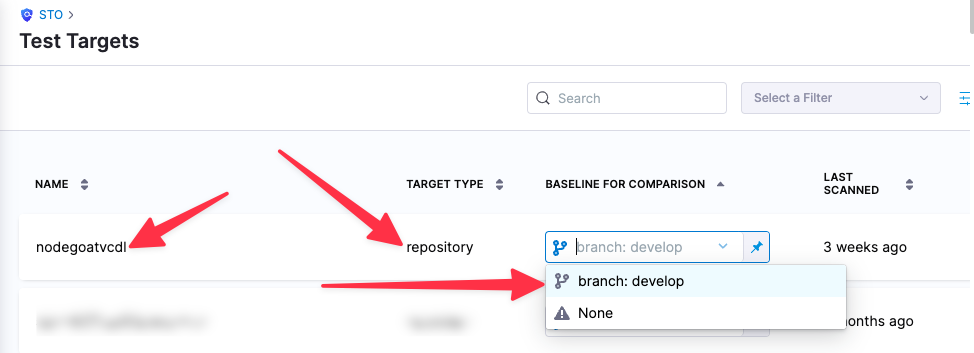
For more information, go to Targets, baselines, and variants in STO.
SonarQube SonarScanner settings
product_name=sonarqubescan_type=repositoryproduct_config_name=default— Runs a SonarQube scan with default settings.policy_type— Enter one of the following:orchestratedScan— A Security step in the pipeline runs the scan and ingests the results. This is the easiest method to set up and support scans with default or predefined settings.dataLoad— The pipeline downloads scan results using the SonarScanner API.ingestionOnly— Run the scan in a Run step, or outside the pipeline, and then ingest the results. This is useful for advanced workflows that address specific security needs. See Ingest scan results into an STO pipeline.
repository_project— The repository name. If you want to scanhttps://github.com/my-github-account/codebaseAlpha, for example, you would set this tocodebaseAlpha.repository_branch— The git branch to scan. You can specify a hardcoded string or use the runtime variable<+codebase.branch>. This sets the branch based on the user input or trigger payload at runtime.fail_on_severity- See Fail on Severity.tool_args- You can add atool_argssetting to run the sonar-scanner binary with specific command-line arguments. For example, suppose the scan is experiencing timeouts due to long response times from a web service. You can increase the timeout window like this:tool_args=-sonar.ws.timeout 300.
ingestionOnly settings
If the policy_type is ingestionOnly:
ingestion_file= The path to your scan results when running an Ingestion scan, for example/shared/scan_results/myscan.latest.sarif.
-
The data file must be in a supported format for the scanner.
-
The data file must be accessible to the scan step. It's good practice to save your results files to a shared path in your stage. In the visual editor, go to the stage where you're running the scan. Then go to Overview > Shared Paths. You can also add the path to the YAML stage definition like this:
- stage:
spec:
sharedPaths:
- /shared/scan_results
orchestratedScan and dataLoad settings
product_domain— The URL of the SonarQube server. Use the value of thesonar.host.urlparameter in SonarQube.product_access_token— The access token to communicate with the SonarQube server. You must create a secret for the token and use the format<+secrets.getValue("secret_name")>to reference the secret. This example references a secret created at the project level. For additional details on referencing secrets, go to Add and Reference Text Secrets.
Go to the SonarQube docs for information about creating tokens.product_project_name—The name of the SonarQube project. This is the also the target name in the Harness UI (Security Tests > Test Targets).product_project_key— The unique identifier of the SonarQube project you want to scan. Look forsonar.projectKeyin the sonar-project.properties file.product_exclude— If you want to exclude some files from a scan, you can use this setting to configure thesonar.exclusionsin your SonarQube project. For more information, go to Narrowing the Focus in the SonarQube docs.product_java_binaries— When scanning Java, you need to set thesonar.java.binarieskey in SonarQube. This is a list of comma-separated paths with the compiled bytecode that correspond to your source files. See Java in the SonarQube docs.product_java_libraries—sonar.java.binariesis a comma-separated list of paths to files with third-party libraries (JAR or Zip files) used by your project. See Java in the SonarQube docs.